Shodan on Twitter: "Not sure what search filters are available? Check out our new filter reference page: https://t.co/kDlGDgpFms https://t.co/bUJX1D8ChQ" / Twitter
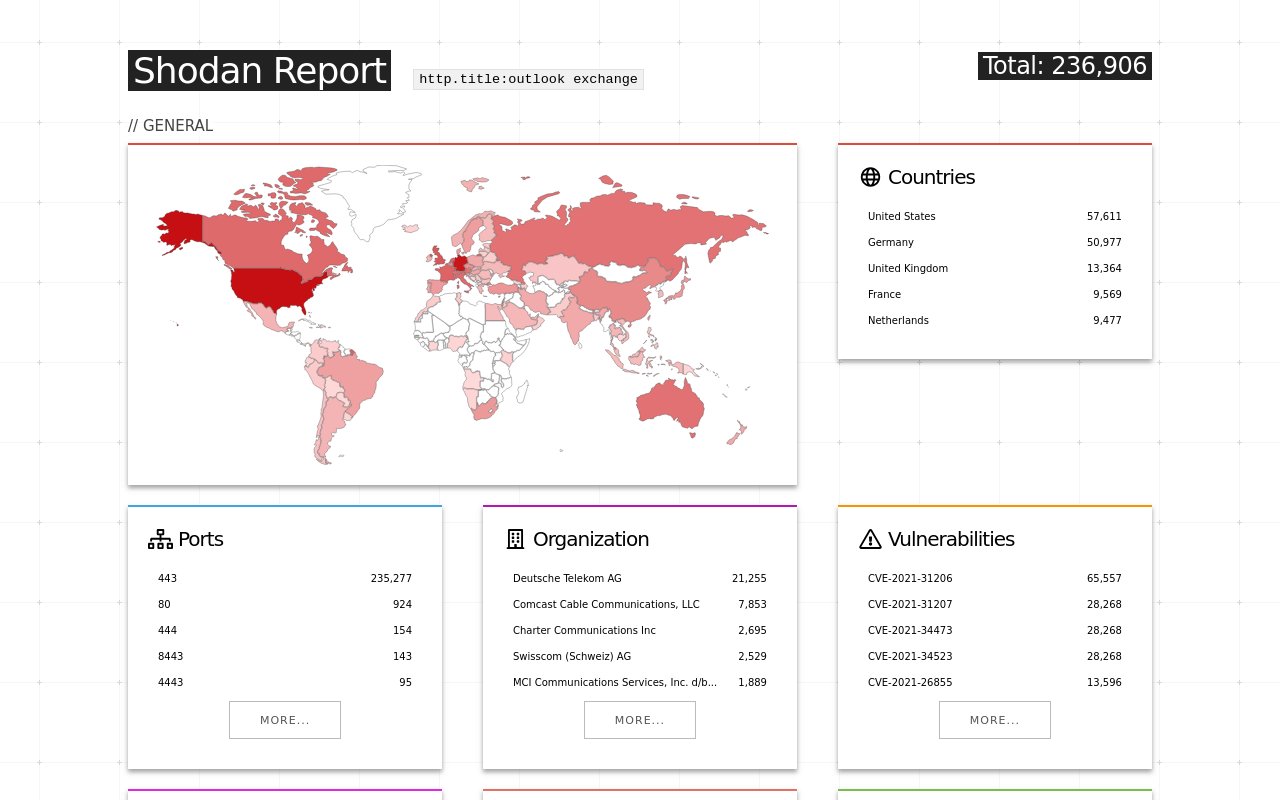
Shodan on Twitter: "More than 18% of Exchange servers remain unpatched for the ProxyShell vulnerability. Nearly 40% are vulnerable to CVE-2021-31206: https://t.co/7yetz9GoJw https://t.co/0r2AOQsibB" / Twitter
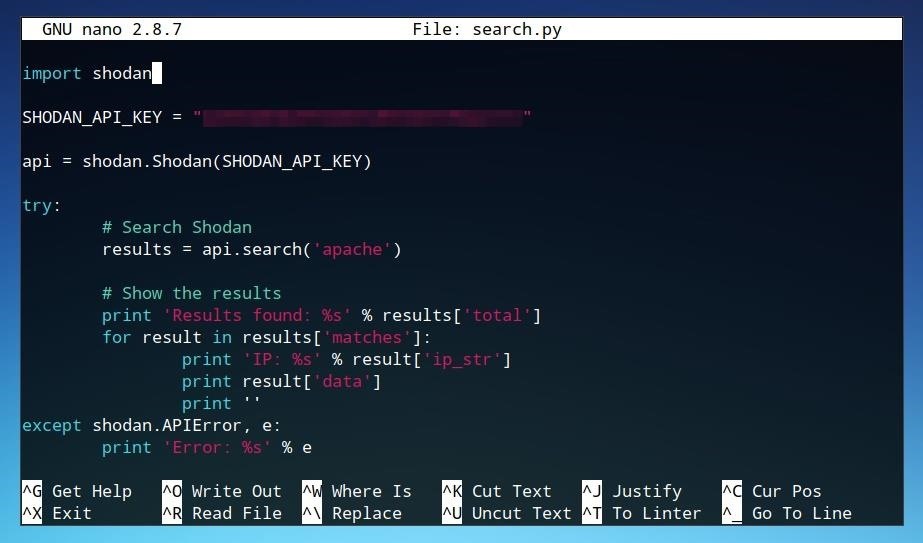
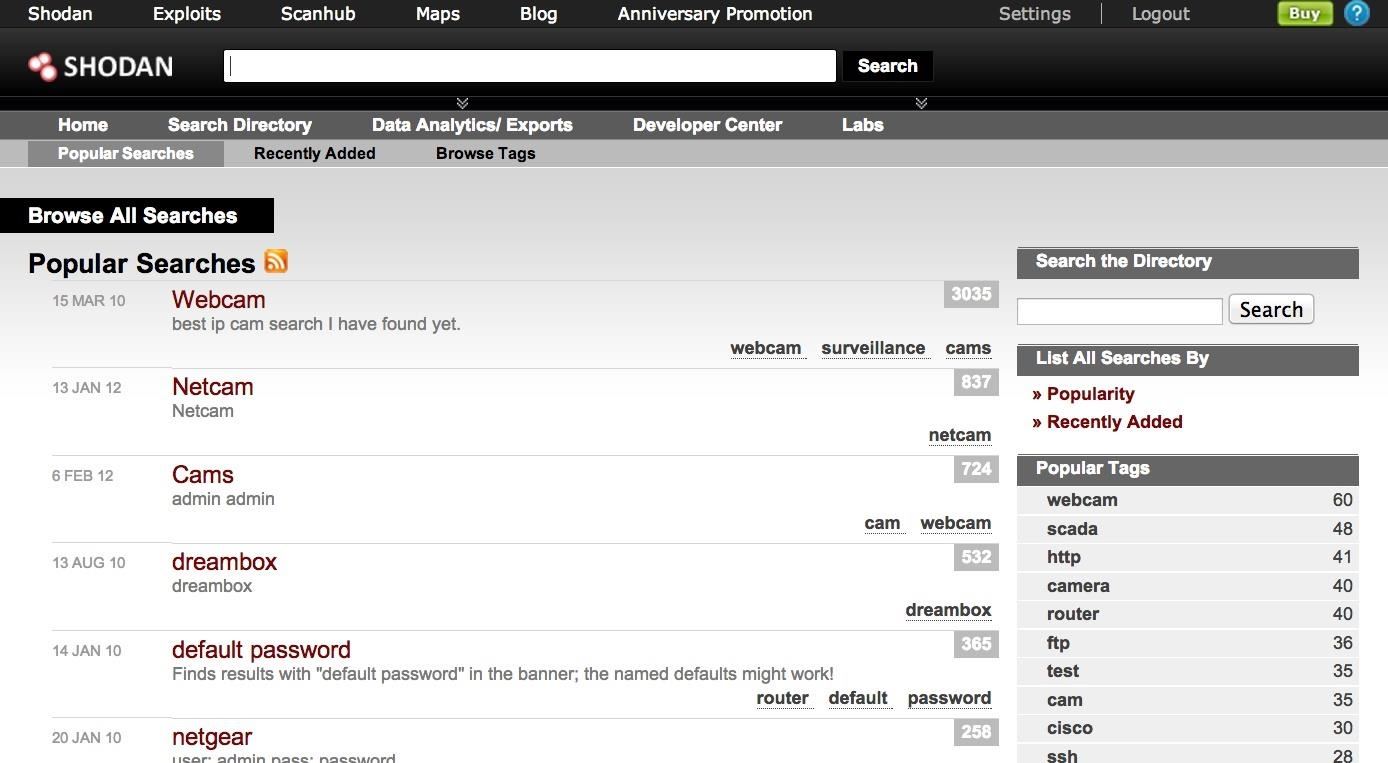
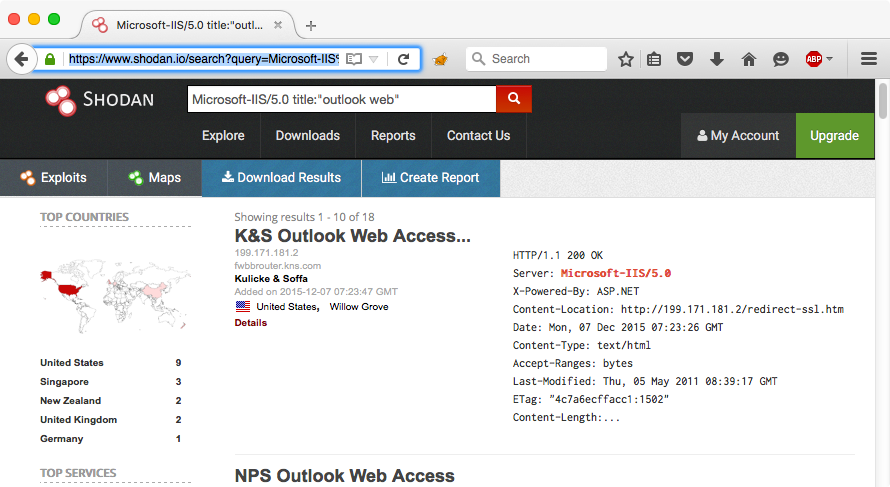
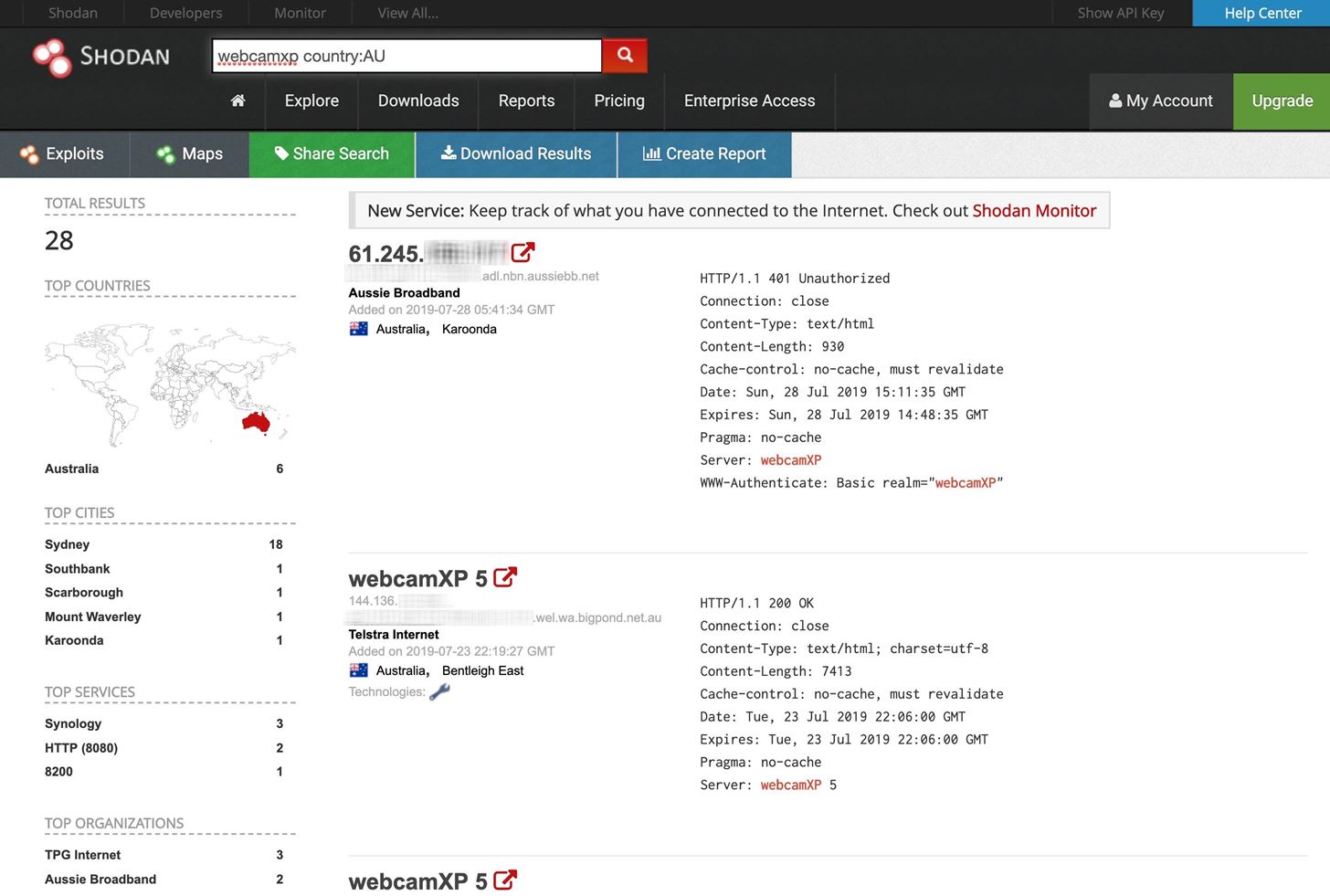
The Hacks of Mr. Robot: How to Use the Shodan API with Python to Automate Scans for Vulnerable Devices « Null Byte :: WonderHowTo
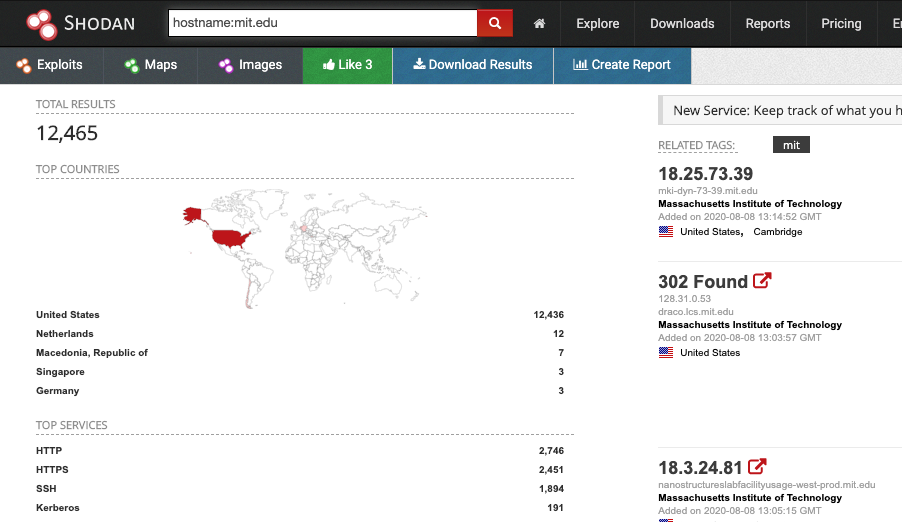
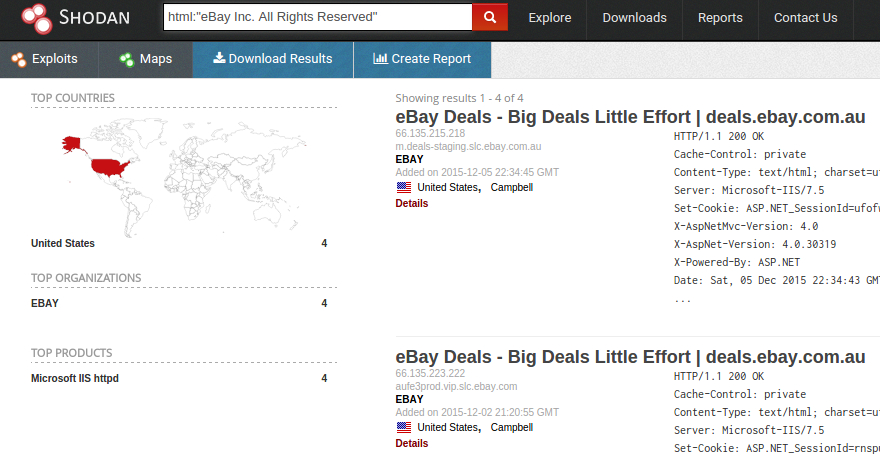
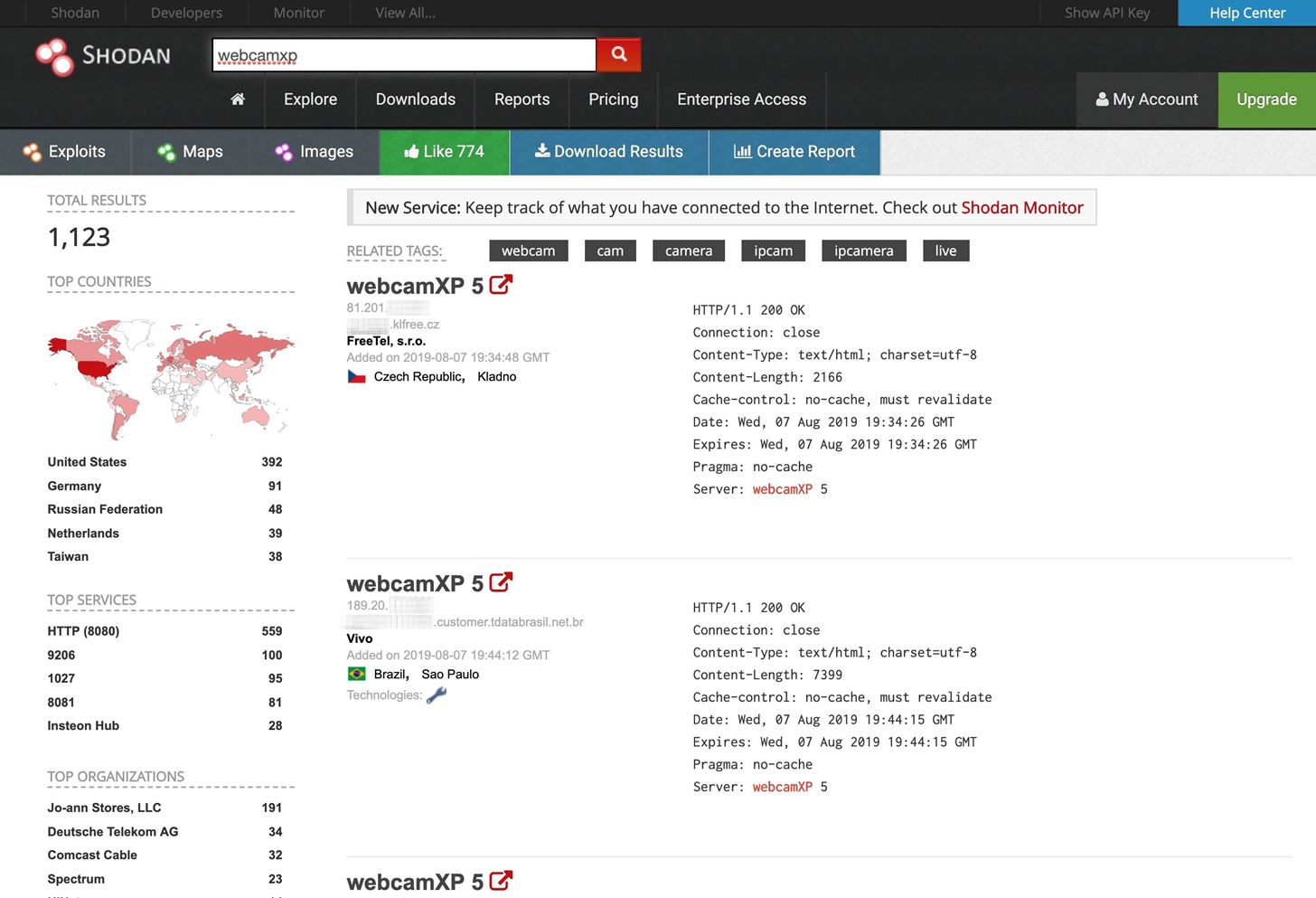
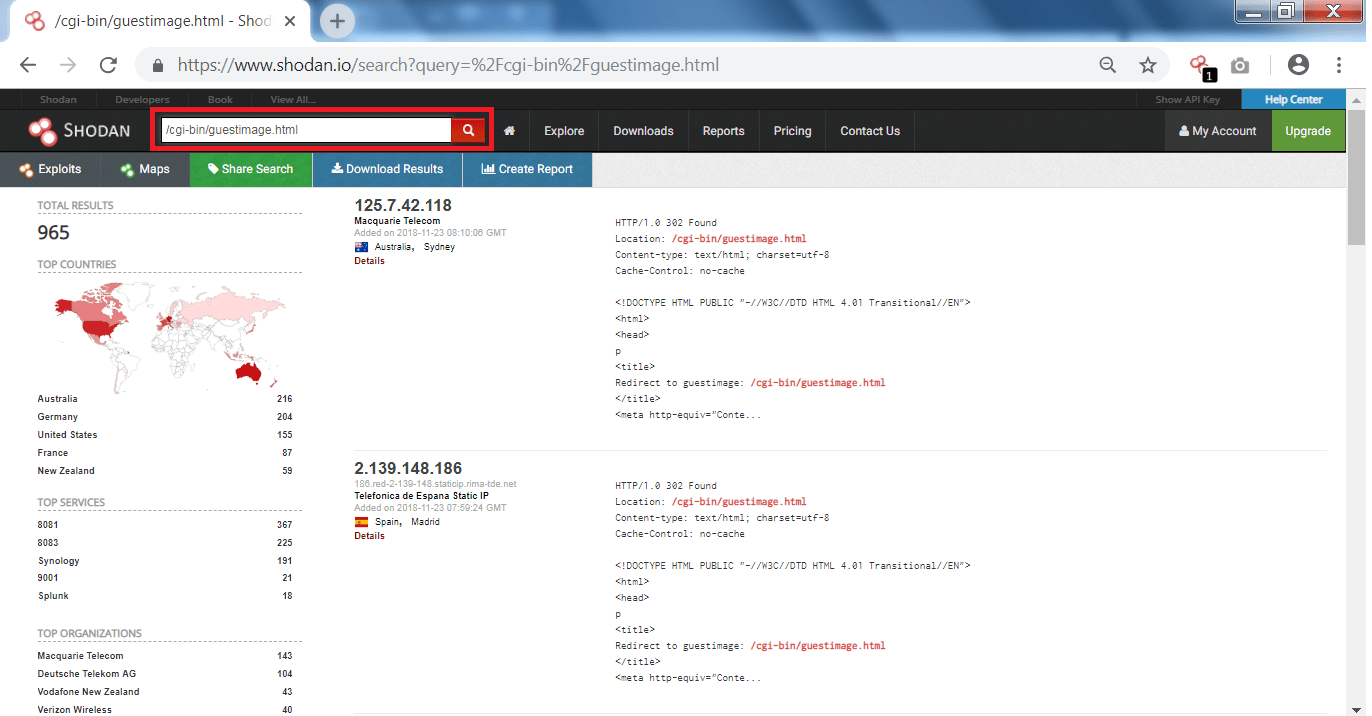
GitHub - jakejarvis/awesome-shodan-queries: 🔍 A collection of interesting, funny, and depressing search queries to plug into shodan.io 👩💻








![Search for Vulnerable Devices Around the World with Shodan [Tutorial] - YouTube Search for Vulnerable Devices Around the World with Shodan [Tutorial] - YouTube](https://i.ytimg.com/vi/oDkg1zz6xlw/maxresdefault.jpg)